According to security researcher Brian Krebs of KrebsOnSecurity, “Facebook is probing a series of security failures in which employees built applications that logged unencrypted password data for Facebook users and stored it in plaintext on internal company servers.”
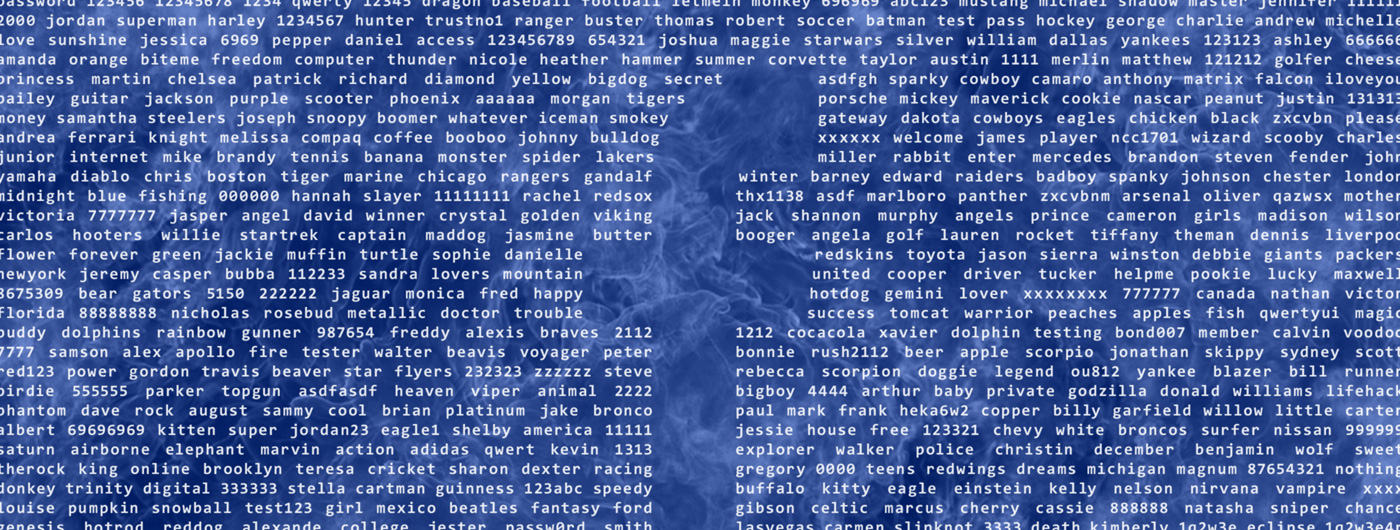
Reportedly, 200 million to 600 million Facebook users had their account passwords stored in plaintext and readable by more than 20,000 Facebook employees. Despite the fact that many breaches are internally triggered by bad actors with inside access, Facebook’s statement seems to say that the situation is not that bad because no passwords were exposed to people outside of Facebook. But, even with only internal access, “we have found no evidence to date that anyone internally abused or improperly accessed” the passwords isn’t the same as no one did.
Ars Technica gets into how this actually happened, “Facebook Lite is a version of the mobile Facebook application 'predominantly used by people in regions with lower connectivity,' as [Facebook Vice President of Engineering, Security, and Privacy Pedro] Canahuati put it. The Android app is most popular in Brazil, Mexico, India, Indonesia, and the Philippines, as well as other countries in South Asia with older 2G and 3G GSM networks—markets where Facebook has experienced much of its recent growth. Lite uses a proxy architecture, with an application server running most of the application code and minimizing the amount of data that needs to be sent to the user's phone. And apparently, because it was acting as a proxy, the server was acting on behalf of users and logging their credentials for use in connecting to other Facebook services.”
Beyond the most obvious takeaway that logs should never include passwords or at the very least encrypt them, this is yet another example of how password security is so complicated that even Facebook, with 2.3+ billion active users, a nearly $500 billion dollar market cap, thousands of software developers, and a professional security team messed it up.
It is also reminiscent of the GitHub and Twitter password exposures. And, considering that 81 percent of hacking-related breaches leveraged stolen and/or weak passwords, this is serious.
Passwords are the weakest link in most applications. But if even if the largest, most well-funded organizations can’t do this correctly, what chance do you have? This why our new PureKit SDK is a gamechanger.
Pure stands for “Password and User Records Encryption” and is based on the PHE (Password-Hardened Encryption) service. PureKit replaces password hashing with a more advanced solution that prevents brute-force attacks on passwords or sensitive data stored in a database and allows developers to instantly render stolen passwords or databases useless without any inconvenience to the end-users. Even better, PureKit doesn’t require a team of security experts to deploy, but can be integrated into your products/services in a matter of hours.
Someday, passwords will be obsolete. Until then, let’s hold Facebook and others accountable for their mistakes, because they truly should know better. Without consequences there are no incentives to improve.
Want to see how PureKit works? Sign up for a free Virgil Security account and then create a Pure app in the Virgil Dashboard. Learn more in the PureKit documentation here.
--
Virgil Security, Inc. builds developer toolkits that solve business problems by encrypting data and therefore lessening legal and compliance liability. Teams can secure their application data with end-to-end encryption, manage devices across a network, and secure passwords and PII in the database using Virgil’s suite of open source SDKs. To learn more, visit https://VirgilSecurity.com.